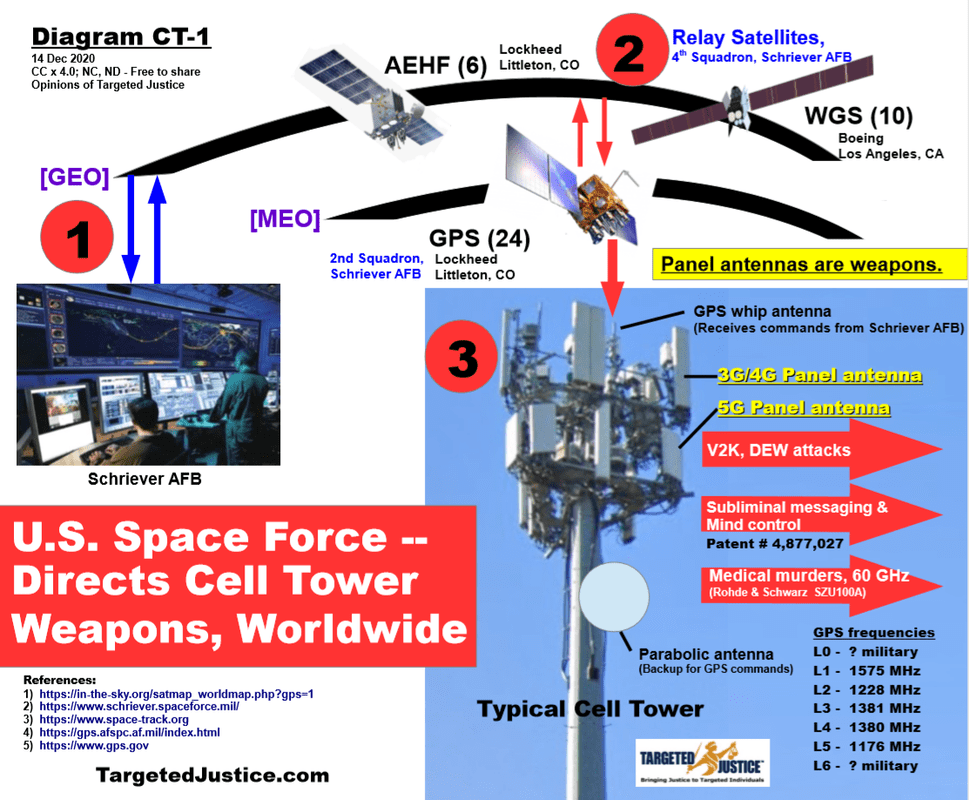
I am proud to say I recently joined the advisory board of Targeted Justice, on which doctors, scientists, lawyers, journalists, a retired police chief, and the former Assistant Secretary of Housing also serve.
https://www.targetedjustice.com/team-members.html

Targeted Justice is the world’s leading resource for Targeted Individuals and Havana Syndrome, full of educational and activist materials, so I strongly encourage everyone to check it out.
https://www.targetedjustice.com
The Deep State, which recruits from the gutter, and destroys its own, doesn’t have a chance.
=======================================================
Return to my homepage, where you can scroll through more articles, by clicking the site title at the top of the page or at www.fightingmonarch.com
Follow my website, which you can easily do for free. That way you can get new articles as they come out.
And please retweet or share as many articles as possible.
Our enemy depends on silence.


































Voices in Their Heads
I have tried to make a story outlining the tragedy effecting our society that uses both fictional and real characters as we try to learn what is wrong with our mindset!
I am not fortunate enough to have first hand documentation that might be provided by the American Psychological association, who might have information from their participation in the cia torture operations overseas.
There are many theories on microwave weapons use, the diplomats in Cuba who were attacked saw traumatic brain injuries inflicted .
The recent reports in veterans today.com speaks quite frankly about ongoing assaults on American civilians.
All relevant links provided
A journey into their world.
Anchorage Alaska
The voices in his head never stopped
Having arrived in Anchorage after his tour in Iraq he at first tried to hide this.
He knew what would happen to his career. He knew he would let down the ones he loved.
The voices would not stop.
As if a light switch being turned on his journey had began.
He would find sleep desperately unable to escape these voices, a radio station only he could hear,
He awoke in the mornings not to the sounds of birds chirping.
He awoke to horrors he had never imagined.
To screams of anguish, screams of pain, screams of death that never ended, unless they were replaced with the ever looping Chatter.
Not one voice, not two voices, at times uncountable voices all Chattering endlessly competing for the airwaves in his mind.
Friends and family and foe alike would join voices of those he had never met, their screams blended with others out of sight, never out of mind.
He was never short for conversation.
They were telling him to join Isis, they were telling him to kill. If this was not enough to fracture his mind, the images, scenes played out in what seemed to be like a video only he saw, accompanied by the audio that only he heard.
Isis training videos.
There was no escape, there was no getting up and walking out of this “theater.”
This theater was in his head.
He was discharged from the Alaska National Guard.
Struggling to hang on to his sanity as if walking a never ending tightrope, was impossible. With much courage he walked into the Anchorage FBI office not knowing where else to turn for help.
He explained to them his mind was being controlled by American Intelligence agencies carrying out these assaults, it was the CIA forcing him to watch these Isis training videos, telling him to murder people in the nonstop Chatter inside his head.
Santiago made it clear he was not planning on hurting anyone, never-less the FBI called the Anchorage Police Department on him and he went in for a mental evaluation.
He would not be joining Isis, but he would soon after his release be taking a short trip.
United States of America
Standing at the mirror, looking at the numerous medals adorning my uniform, I thought it must be done. If we are going to protect innocent men and woman in America from the terror abroad we must be willing to use microwave weapons on our own civilians!
Air Force Secretary Micael Wynne walked out the door to the waiting reporters.
If we are not willing to use it here against our own citizens, then we should not be willing to use it in a wartime situation.
“If we hit someone with microwave weapons and it injured them a some way that was not intended, I think we would be vilified in the world press”, if we used these weapons on our own men and women first.
Cheering erupted in the room, this man should run for political office some of the reporters noted, what leadership!
Looking out at the reporters Wynne was relieved to see this reaction. How had he have been foolish enough to question this decision he wondered.
He knew these weapons could weaken people when they were hit with the pulsing beams, they were also useful in jamming electronic communications,
This is what America needed, and he was here to serve his country, protect the people of the Homeland he thought walking from the podium.
Parkland Florida
It had began at a young age. Some of his first memories traumatized him. That was so many years ago he thought sitting staring into space, tears running out of his eyes.
The voices never stopped.
BURN KILL DESTROY
Burn, Kill, Destroy
burn, kill, destroy
The Xanax had little effect
The screams at night lingered through the days
Only replaced by constant Chatter
BURN KILL DESTROY
Burn, Kill, Destroy
burn, kill, destroy
Kill me. Just f—ing kill me. F—
He screamed as he emptied the bottle into his mouth.
The pills were not Xanax
His Journey had just began
Newtown Connecticut
Special Agent in charge, sits in his SUV going over his notes to decide what to put in the reports.
Although the Lanza kid did breach many levels of national security computers at a young age, he seemed like the average all Americans youngster, actually a little bright for his age.
His collection of violent videos games, along with a home filled with rifles guns and ammo, was of course every Americans right, the rights he took the oath to uphold, he thought to himself.
His mother checked out as well, the report from homeland security that had been “faxed” to him, confirmed the fusion centers, nsa, police, had never received a suspicious activity report.
She was employed with at the local elementary school, Sandy Hook, where she worked with Karin Halstead.
Karen had checked out as well, her ex husband was involved in fema emergency management training, as well as the Fire Chief for Sandy Hook, just a block from his ex wife.
His First Responder daughter Karen worked with William as well.
It was mentioned in the report that we might need to hold active shooting drills both at and near Sandy Hook because we have seen so much violence in this community.
William could help plan these out and protect this community better he thought.
With everything checking out he glanced down at the picture of 3-4 year old Adam Lanza grinning, he will fill out one day he thought, if he’s going to carry around all the ammo and guns he’s pictured with.
Washington
He lay in his hotel alone, the pounding in his head never stopped, the ringing in his ears seemed to decrease when he showered.
But the microwave weapons seemed to be above him now, he got up to nervously glancing out the window when he hear the horn honks.
The pounding in his head quickly replaced by the pounding on the floor coming from the room above him.
He layed down again slowly drifting off to sleep as the police sirens faded into the distance.
It never ended.
In a later interview, a friend of his in Fort Worth Texas said “he always thought someone was trying to hurt him.”
The jets roaring overhead as they made there way back to Lockheed Martin after more test flights.
Aaron awoke to the screaming voices coming from the ceiling, accompanied now by the pulsing and pounding reverberating through his whole body,
He might not sleep again for many days he thought to himself, laying still, staring at the ceiling, trying not to hear the screams.
Waco Texas
She looked nervously at her daughter shaking and crying, covering her ears.
The spotlight burst through the window again. The sounds never ended.
This time it was hours of nonstop screaming, the sounds of rabbits being slaughter filled the air, coming from the FBI or military personnel that had surrounded the compound.
She gently ran her fingers through her weeping daughters long hair, closing her eyes she began to pray.
John Hopkins University
The Owl secured in the tube the bone saw went to work. Screwing and gluing the electrodes in place was easy work he thought, wrapping up the task ahead of schedule as he made his way to the parking lot for a quick cigarette. It should be interesting to review the data in the coming weeks.
The owl gripped tightly by the tube he was confined in stared into the laboratory as the sounds filled his brain and the flickering lights filled his vision, seconds went by as hours.
Fort Detricks Maryland
Fort Detricks
He flashed his badge as he drove through the gates main entrance. Fumbling with his keys he thought to himself, I doubt they left the door open again with all this going on, chuckling.
Glancing at his watch he hurried his pace, opening the door to his office the paperwork was sitting on his desk where he left it. Grabbing it quickly he made his was to his truck, settling in for the hour plus drive.
The sun blinding him as he left the parking lot he put on his dark tinted glasses, adjusting them as he drove off.
Tallahassee Florida
He sat at his desk looking at his law diploma, the LED headlights hit his window again.
He did not know how to make people believe him, stalking and harassment every day and every night.
If the accounts are true, he made a serious mistake.
How could the pain and suffering of others help relieve his own pain.
Wasn’t there another avenue that he could have taken.
He put down the cell phone, glancing at it as it glanced back at him, after leaving a short message for his acquaintance.
“I do not want to die in vain”
He had found out about the cointelpro counterintelligence community policing operations years before. Targeted individuals were often do traumatized they offered little help. His post on social media, Youtube, Twitter, Facebook we’re blocked, shadow banned or hacked.
The NSA data hacking or “surveillance” that all telecommunication corporations participated in left his smart devices often wiped clean of the evidence he had gathered.
Sydney Australia
She sat locked in her own home. Little difference it made to her, her home had been her prison for many years.
She had fled from America thinking she could escape.
Unaware that these operations were now carried out in every country in the world.
Surveillance technology sweeping the globe as the 911 attacks had given reason to monitor civilians, the interlinking of intelligence and policing agencies across the globe had created a well functioning Stasi like policing network which targeted any “domestic terrorist threat.
She glanced up at the magnets hanging above her head suspended from the mobile she had made, watching them swing in the air as she tried to tune out the voices.
The magnets did not stop them.
She counted as she breathed in filling her lungs.
She held her breath as she again slowly counted.
She slowly exhaled repeating this again and again.
The scatter frequency playing on her bone conducting head phones competed with the voices.
She knew better then to respond.
She tried to clear her mind.
Fort Worth Texas
I stayed in Fort Worth a extra month after arriving to document the harassment taking place. Dave was staying in the same hotel.
Boron, activated charcoal, tumeric, heavy metal detox, infrared saunas all seemed to help the constant ringing in my ears that often changed tones, there was little to do about the pain which seemed to coincide with the high readings on my EMF 390, luckily the worst that had happened so far was the heart palpitations, physically that is.
I guess if these microwave weapons can keep a bear at bay, they might work on humans too, little matter, where was one to go in this age.
The stay at this hotel did not see the last of these attacks, nor we’re they the first.
The advice from the other targeted individuals neither helped or seemed to effective when utilized.
I tried to move around a lot when this happened, take long baths or showers which also reduced the ringing in the ears or just following my EMF meter to the lowest reading as I carried my blanket with me I would sleep in.
The closeness of Lockheed Martin was dually noted.
The planes roared overhead early morning till mid day this day.
Just a ten minute drive to the base and you could see little.
I recorded the sitting cars shining their LED lights on me when I smoked, and the constant parade of firetrucks, EMT’s, and of course the honking horns.
Forty to a hundred honks at a time, usually around forty but at this hotel a truck had pulled into the next lot and endlessly honked their horn.
I confronted many of the occupants of the vehicles, the officer stationed at a airbase refinished to identify himself, open his door, tell me the name of his commanding officer or where he was stationed.
The guy sitting outside of a hotel room where I later stayed with another targeted individual told me his cars horn was honking itself?
The guy that almost ran me off the road in Arlington appeared drunk at the time, extremely angry in the video when we “spoke” the policemen apparently to busy to help, I left.
The 6-8 men that surrounded me with yard tools at night when I was at a RV park in Arlington Texas with Jason Foust who is a member of Targetedjustice.com
actually called the police on me after I again walked down to see what the commotion was all night, after previously following Sarah’s dog, tracking the scent he caught after unchaining him following noise harassment, he immediately led me to the street ever 3-4 of these guys were standing but proceeded to walk to the residence in question with me following them. I left without speaking after they entered residence without trespass..
As usual I posted the videos to numerous sites knowing my hotline account was apparently shadow banned.
Rick and Cindy Klrich has endured the noise harassment for years, I wondered if they were victims of microwave experimentation as well?
I placed my cell phone in the small toolbox I had lined inside with neodymium magnets closing it tightly.
This apparently stopped the microwaves for the text messages would rush in when opened. The microwave oven had not stopped the microwaves from getting to the cel phone, If these were scalar waves I just wasn’t sure how to stop them.
I had started a website in 2008 scalarwarfare.com, yet my attention was directed elsewhere as I had been researching the escalating violence seen in active shootings for many years.
I again had my research redirected after linking many events in the preceding years to these attacks, and having numerous assaults take place in Anchorage Alaska in 2008-2021
http://web.archive.org/web/20210128030005/https://www.targeted.one/
The box should at least stop the ultrasonic radar tracking.
I guess it really didn’t matter, but it felt good to take any action at all.
Anywhere USA
Looking at the schedule, the date read the same.
Society was finally excepting the many years of community and school involvement. I glanced over at the retired police investigator, he had a busy schedule.
It was lucky for the production company that so many knowledgeable individuals were gathered to promote such a diversity of ideas to American children.
Working hand and in hand with the community policing instructors that helped teach children how to police our nations streets, we have alway felt privileged to spread these messages, though some have seen much tragedy in their lives.
This is a work in progress, saving as I proceed.
This is not a exact accounting of course, links provided. Some name have been changed.
Santiago: https://nypost.com/2017/01/07/airport-shooter-to-fbi-voices-in-my-head-telling-me-to-join-isis/
United States of America
https://www.nbcnews.com/id/wbna14806772
Nikolas Cruz: https://www.nbcnews.com/news/us-news/parkland-shooting-suspect-nikolas-cruz-spoke-voices-says-he-attempted-n898151
Newton Connecticut
https://www.newsweek.com/day-fbi-knocked-adam-lanzas-door-226657
Aaron Alexis
https://www.usatoday.com/story/news/nation/2013/09/17/navy-yard-shooting-aaron-alexis/2825749/
Waco Texas: http://www.cnn.com/2000/LAW/05/10/waco.thibodeau/
John Hopkins University
https://headlines.peta.org/johns-hopkins-university-owl-experiments/
Myron May
https://external-content.duckduckgo.com/iu/?u=https%3A%2F%2Ftse1.mm.bing.net%2Fth%3Fid%3DOVP.uhuB7-izdLhYnB1APSpEBwEsDh%26pid%3DApi&f=1
Rick and Cindy Klrich
http://krlich.com/
Sarah Degeyter
ExposingGangstalkingintexas.wordpress.com
Anywhere USA
Click to access kirkland-catalog-2021-22-web.pdf
Veterans Today: https://www.veteranstoday.com/2021/06/21/targeted-individuals-now-that-we-know-its-real-will-someone-finally-do-something/
https://www.veteranstoday.com/2021/11/13/nsa-mind-control-outlined-in-document/
Gina Kirkland trained at Galvin De Becker which provides security to the Royal Family, Zuckenberg, Supreme Court justices, cia, etc if anyone wants to research this?
Images: https://www.nbcnews.com/news/all/havana-syndrome-likely-caused-microwave-energy-government-study-finds-n1250094
American Psychological Association
https://time.com/3841576/american-psychological-association-torture/
https://www.veteranstoday.com/2021/11/13/nsa-mind-control-outlined-in-document/
https://en.wikipedia.org/wiki/Project_CHATTER
© on Nov 19 2021 12:27 PM PST, Keith Lankdord
Read more →
LikeLike
Did MK-ULTRA CANDada Do The Montreal Massacre n Are THEY MISOGYNIST Sexcists That Did The “Drive Down Sidewalk/Shooting in Little Italy/Greektown In Toronto?;):(
RadicAll Rickery Raymond ME/WE
LikeLike
[https://m.youtube.com/watch?v=990k-5Jm5aA][https_m.youtube.com_watch_v_990k-5Jm5aA]
Did MK-ULTRA CANDada Do The Montreal Massacre n Are THEY MISOGYNIST Sexcists That Did The “Drive Down Sidewalk/Shooting in Little Italy/Greektown In Toronto?;):(
Oliver British Columbia CANDada Biolog-i-CULL Warfare Meningitis With South African Pfizer PseudoscienceDAIRYFAIRYp$ychiatrist?
RadicAll Rickery Raymond ME/WE
https://fightingmonarch.com/2021/11/16/fighting-monarch-joins-forces-with-targeted-justice/comment-page-1/#comments
[https_m.youtube.com_watch_v_990k-5Jm5aA]: https://m.youtube.com/watch?v=990k-5Jm5aA
LikeLike
Methods to Silence : Updated
OINTELPRO and Being Assaulted by NWO OSS CIA attacks on the USA and world
Methods used by criminals in USA government infiltrating Espionage positions to silence whistle blowers Dorothy Kilgallen, Ted Gunderson, Jen Moore, Ed Donegan, others
Most of this from TARGETED PUBLICATIONS
Surveillance and Harassment Survivors Alliance
surveillancesurvivors.org
TERMINOLOGY and use of Targeting Individuals including Slandering them as retarded and into hostile and explotitave asset management
TARGETED PERSON: An individual who has been placed into a program of psychological and often physical warfare tactics which are orchestrated by criminal organizations, corrupt politicians, government agencies, security companies, law enforcement personnel, colleges, doctors, scientists and corporations.
COVERT HARASSMENT: Also known as gangstalking or organized stalking, is a highly criminal campaign directed at a targeted individual that aims to destroy an innocent person’s life through slander and carefully executed psychological and physical assaults.
SLANDER CAMPAIGN: An intentional, premeditated effort to undermine an individual’s reputation, credibility, and character. (his rationality or credibility or desirability as a news source may also be called into question and discredited in value)
POISONING, D-E-W, CREATING UNSAFE CONDISTIONS AND ACCIDENTS, BOSTON BRAKES: Also know as DEW, is a ranged weapons system that inflicts damage at a target by emission of a highly focused energy, including (but not limited to) radio, laser, microwave, sonic, and particle beams. Raw Source radiativce materials are also planted and used. Do not get an XRAY in the USA.
VOICE TO SKULL TECHNOLOGY : Also called V2K, V2S, or Voice of God Weapon, is a weapon used for transmitting voices with low frequencies and can be used to induce or manipulate dreams or deprive the target of sleep. Some believe this is true and is based on psyichs based EMF, cognition, and hearing.
Books on the subject of cover opps dirty wars
Ramblings Of A So-Called Paranoid Schizophrenic
Extrajudicial Execution
In his own words, a Targeted Individual (TI) exposes his tormented life and the heartless, sadistic and invasive methods used covertly to undermine his credibility, cause illness and excruciating pain, ruin him financially, tear apart his family, drive him mad and lead him to consider suicide. This dramatic and cautionary tale may seem extreme and far-fetched, but thousands of other Targeted Individuals throughout the world are suffering in silence right now. In this candid account, the author describes the psychological, emotional, mental and physical torture that he has endured for over six years, hoping that he will survive long enough to see this book in print.
Notes From An Engineered Life: A Book Of Hope In Mind Controlled America
An honest look at the engineering of a life using modern psychotronic electromagnetic technology as well as infiltration and trauma… MKUltra meets Transhumanism. Honest Reaction from the life of a military industrial complex non consensual test subject.
The Day The Fish Came Out (Film 1967)
Fictional, the movie about the time of the Robert F. Kennedy assassination is conceptually very important
The film, set in 1972, was inspired by an actual incident which occurred on 17 January 1966: a B-52G Stratofortress collided with a KC-135 Stratotanker over Palomares, Spain, and four B-28 FI 1.45-megaton-range hydrogen bombs aboard the B-52 were briefly lost.
Life on the remote Greek fictional resort island of Karos is forever changed when atomic bombs are dropped there by a NATO plane rapidly losing power. Life on the island is so bleak that the inhabitants stage a mass exodus on news that Denmark has opened Greenland to Greek emigration. The pilots drop their payload – which includes two atomic weapons and a mysterious box called simply “Container Q”
The pilot and navigator of the lost bomber scour the island like vagabonds. Unknown to the pilots, the Americans have already deployed their own operation: a team of agents disguised as resort developers. The pilots are unaware of the fact that American agents are also on the island searching for their cargo.
The significance of the plot is that MKULRA is covering up military industrial CIA assassinations and long term operations by using espionage teams to target locations and people who pose an informational threat to US misconduct and assassinations including overthrow of the US Government and its elected offices by the Military Industrial Complex.
The mechanisms involve an initial element of a circumstance which by contrived evidence or actions create an ambiguous appearance, the ambiguity is in favor of the victim being stalked by paid actors but the paid actors will outside of Due Process protections slander the stalk victim behind the stalk victim’s back by resolving the ambiguity of the original scene against the Stalk Victim, often seeking victim funds from a third party such as the Department of Justice or others while the Stalk Victim is left out of the loop as the stake holder in being accused.
Often ethnic, racial, religious, or sexual orientation motivates the attack and if the Stalk Victim attacks a Stalker it adds to the perception the Stalk Victim is in the wrong against the Stalker who was attacked by the Stalk Victim.
ETK Introduction Dr. Eric T. Karlstrom P.O. Box 54 Crestone, CO 81131 email https://911nwo.com/
What is Gang Stalking a Targeted Individual? Targeting of Individuals by the US Government for Subversion, attacks, etc.?
By Professor Eric Thor Karlstrom, Ph.D https://erickarlstrom.com/
“Gang Stalking” is, very likely, a disinformation term created by U.S. intelligence agencies. It refers to the intense, long-term, unconstitutional surveillance and harassment of a person who has been designated as a target by someone associated with America’s security industry.
Such operations have nothing to do with criminal gangs. Official domestic counterintelligence operations of this type are – apparently – perpetrated by federal agents and contractors, sometimes with the support of state and local law enforcement personnel. The goal of such operations – in the parlance of counterintelligence agents – is to “subvert” or “neutralize” an individual deemed to be an enemy (or potential enemy) of clients or members of the security state. Arguably, the most accurate term for this form of harassment would be “counterintelligence stalking.”
Espionage Agencies target people for subversion of careers, housing, family, jobs, etc., thorugh illegal acts and under-cover operations.
A Simple Definition
Under Occupational Health and Safety laws, individuals are being flagged and placed on community notification lists. This is happening without the targets knowledge. In many countries these community notifications are being used by companies and others to target innocent individuals such as whistle-blowers, the outspoken, etc. In conjunction with these notifications, companies and others are in some cases using a practice that was used in the former soviet union called the psychiatric reprisal. This is used as a means of retaliation, blacklisting, silencing, or controlling members of society. Once on the notification system, warnings about the targets are sent out to every individual the target comes in contact with, thus poisoning their associations, and socially annexing the targeted individual.
Gang Stalking is a systemic form of control, which seeks to destroy every aspect of a Targeted Individuals life. Once a target is flagged a notification is sent out to the community at large, and the target is followed around 24/7 by the various communities that they are in.
The goals of Predatory Gangstalking of an individual are numerous. Predatory Gangstalking is intended to deprive someone of their freedoms and rights. It destroys a person’s privacy and control of their own environments. It is intended to create distress, disrupt all relationships, deplete person’s resources, destroy one’s physical and mental health, and inflict great overall long term suffering. They interfere with a target’s sleep thereby producing chronic sleep deprivation, as a strategic tactic. They employ a variety of interactions with the targeted individual which are likely to produce accidents and various forms of illness. One of the main weapons they use for their own protection and to enable their success in gangstalking is to manipulate the target’s life in such a way as to cause them to lose their credibility with others. This is usually the first objective reached. After that, gangstalking the target involves only minor risk. Notably, people who become involved generally stop caring about the abuse by either turning a blind eye or actively joining in. While others, though concerned for the target, become too frightened to speak out or come to believe the propoganda that the target is mentally ill and needs ‘this‘ help.
Predatory Gangstalking also involves provoking “accidents” and consequences of harm to the target. Predatory Gangstalkers will surrounding a target’s moving vehicle and attempting to force them off of the road when they are stressed and exhausted.
Worse, these tactics will be employed after tampering with a targeted individual’s vehicle. Predatory Gangstalking is very serious business. Predatory Gangstalking is, at the least, psychological violence, and at most, it is a protracted sadistic sociopathic domination and calculated destruction of an innocent human being for reasons of pleasure, power, and social control by a group predatory stranger.
Target Selection and Targets of Value or Interest
Gang stalking apparently targets American citizens deemed to be dissidents or whistle-blowers (and perhaps potential dissidents and whistle-blowers), although others might be targeted for other reasons – such as for experimental or training purposes. For perspective, it should be remembered that for two decades the CIA performed secret illegal experiments on U.S. and Canadian citizens in the infamous MK Ultra program of the Donegan family comes from, the atomic bombing of Japan, atomic testing and DNA, behavoiral research on FOXP2 gene. Those experiments included physical and psychological torture.
A lot of accounts by self-proclaimed targets of gang stalking suggest that people are often subjected to severe long-term harassment simply because they crossed someone connected with the agencies and security firms which perpetrate such operations.
Harassment (a.k.a. “Subversion”) Tactics
In counterintelligence, to “subvert” or “neutralize” an enemy is to make it impossible for that enemy to go about his business. Gang stalkers seek to keep their victim in a constant state of agitation and hyper-vigilance so that he or she will find it almost impossible to function.
This serves multiple purposes. For one thing, it makes it hard for the individual to pose a threat to the client of the gang stalkers – whether that is a corporation or a government.
Note that – as discussed in detail elsewhere in this website – the distinction between corporations and the government is often meaningless in America, given the vast industry of private intelligence contractors with secret clearances, the use of the FBI and other agencies to serve corporate interests, and the lucrative revolving-door nature of employment between the public and private spheres in law enforcement and intelligence. This is another obvious purpose of gang stalking: income for the perpetrators.
Comments by Edward Donegan
ETK will introduce Paid Actors system of assaulting Stalk Victims harass, sabotage, and destroy the lives of a Stalked person.
The cheifmost position the Stalkwer operate from is position of power, gaining Government offices, and holding private business, operating detention facilities such that people are not transported to Due Proccess hearings, Identification are switched out, camera systems are turned off or Hospital IDs are NOT used and something ambiguous is, etc., and personnel of these institutions are recruits selected for duplicitous activities undermining their assigned jobs and procedures.
This is especially dangerous since criticizing (calling out a stalker) lands the stalk victim in the stigma of a crazy conspiracy theorist.
So before getting back to ETK here is some more data I will post from other long term stalk victims.
End Ed Donegan comments and returning to ETK.
PsyOps trying to make business for itself, pissing people off, playing with people’s perceptions, throwing critics in Loonie Bin
Ed Donegan offered Terms which describe GangStalk methods
Functionality
FIXING ON BEHALF OF POWER HOLDERS: The “plumbers” operators go in and undercover fix situations politicians need fixed by altering appearances, outcomes, lives, and even facts which are derived from staged events that did occur but did not occur naturally.
PREDATORY USE OF FINANCIAL CLOUT: Owners of property are its self policing and when help is needed they can call State (Government) police. Use of financial power by criminals can create a lawless reservation in which the owner will likely have the defacto relationship and credibility with police and has certain Common Law type leeway as Shopkeepers on their property such as assaulting other to protect property or remove trespassers, and offer selectively create logs evidence about the property held and select employees who wok on the property. Punch is a synonym of clout. As a proper noun punch is (British) a glove puppet who is the main character used in a marionette punch and judy show. As a noun clout is influence or effectiveness, especially political. As a verb clout is to hit, especially with the fist.
INDIGNIFICATION: Persons or business that are threat may be slandered, indignified by unjust smear tactics, and worth of targeted person hijacked by others via Espionage capabilities surveillance or Conspiracy against Rights including political, intellectual, speech, or religious rights. Selecting In, Out, Down. Selecting Down is a Card Trick of Con Artist who can move a card by slight of hand to a lower place in a deck or to the top of the deck.
ASSASSINATION BY BRINKSMANSHIP: So offense or existential threat conditions or such irreversible harm can be manufactured for the Stalk Victim a lethal and losing flash-fight fight may still result and cost the Stalk Vitim his or her life. “Brinkmanship involves the introduction of an element of uncontrollable risk: even if all players act rationally in the face of risk, uncontrollable events can still trigger the catastrophic outcome. In the “chickie run” scene from the film Rebel Without a Cause, this happens when Buzz cannot escape from the car and dies in the crash.” From Wikipedia the free encyclopedia/
The name “chicken” has its origins in a game in which two drivers drive toward each other on a collision course: one must swerve, or both may die in the crash, but if one driver swerves and the other does not, the one who swerved will be called a “chicken”, meaning a coward; this terminology is most prevalent in political science and economics.
The name “hawk-dove” refers to a situation in which there is a competition for a shared resource and the contestants can choose either conciliation or conflict; this terminology is most commonly used in biology and evolutionary game theory. From a game-theoretic point of view, “chicken” and “hawk-dove” are identical; the different names stem from parallel development of the basic principles in different research areas.[2] The game has also been used to describe the mutual assured destruction of nuclear warfare, especially the sort of brinkmanship involved in the Cuban Missile Crisis.
TIME CONSUMPTION : Those like myself who wish to build an intellectual Natural Law Philosophy Scientific Epistemic fabric of political philosophy. moral philosphy, dirved from Natural Rights theory. Causing harrassing fights which consume time is an FBI system for disrupting “radicalism” by distracting activities and even distracting noise or other harassment.
PLAUSIBLE DENIABILITY BY USAGE OF GEHLEN ASSAILANTS: Reinhard Gehlen, Nazi head of intelligence on the Eastern Front war effort of Nazi Germany. He pionered targeting regular individuals or organizations that Espionage agencies could act through thus remaing publicly out of the picture but bringing about Espionage agency desired ends. “A new biography traces the pathology of allen dulles and his appalling cabal . Dulles also led the push to save Reinhard Gehlen, Nazi head of intelligence on the Eastern Front and a genuine monster, from any post-war justice. Dulles then made certain Gehlen and his spies received a cozy embrace from the CIA, and helped push him to the top of West Germany’s Federal Intelligence Service.” -The Intercept
MALADMINISTRATION, ROAD BLOCKING, AND DOUBLE-AGENT GRAMMS : Bad Faith harrassment of Targeted Indivciduals is achieved by Double Agents who pretend to be neutral parties acting in Good Faith but instead in bad faith make up reasons a lease will end, etc., with excuses like “a new roadway is planned, etc., so, unfortunately, it seems you home will be affected and you will have to move.”
SOCIAL SABOTAGE: The Gang Stalkers will mob any new potentiall association in life and gossip destroy any fruitful result of the desired new association, and in fact often the gossipers will suggest characteristics or property of the Stalk victim be obtained from the Gossipers instead, thus passing by the Stalk Victim in the roadway forward.
PREREQUISITES SABOTAGE OR DEPLETION: Peaceful environments, Sailboarding on a nice day, non threatening public locations, quiet for work, all go into effective mental states and normal life activities. Toxifying all of this creates frantic emotions and hassled frustrated struggles. I Ed Donegan have to MEET people by first warning them the FBI is stalking me and SOON they will Stalk you and you are now in a fishbowl and your friends may be too. Nice start to things.
SLUSH FUNDS: Often the GangStalk is part of Shadow Government and includes lucrative illegal profits. Recruiting operatives into the program under various pay-ff methods allows the illegal operation Human Resources via ensuring recruits will be influenced by personal gains or desire to participate.
STAR CHAMBERS, SURROGACY, IDENTITY THEFT AND COFUSION, MISREPRESENTATION BY CONSERVANCY OR SURROGATES: Blind Conservators or Misrepresentations behind the scenes who work in cahoots while a Stalk Victim is left out of proceedings though is the stakeholder in the outcome, the Shadow Gov works behind the Stakeholders back and protects itself.
STATE ACTS INCLUDING ELDER ABUSE BY MALICIOUS ADMINISTRATION: Hostile abusive 3rd party agency is created to operate as a racket exposing “beneficiary” of the Trust Fund or Conservatorship to crime. The actual interest of the agency placed in charge and is to protect the wealthy by dehumanizing accusers as mentally ill or deluded and holding them without trial in elder abuse conditions of predatory psychiatry and asset management or detention. This book The Great Treason asserts Gangtalk wrestled away artistic works and Britteny Spears and Tom Clancy via and myself Edwad Paul Donean by hostile and abusive conservatorship.
Trespass
Generally Human identity, property, rights, and protection from assaults and protection from harassment is built into modern societies.
The Gangstalk sets up getting control of an environment like taking over a local business then starts forms of trespass such as unwanted and maliciously motivated conversation that is both harassing and a threat from a fraud perspective such as photo-boming a Stalk victim near a security camera in the in the store by adding a child in who is being abused,in such as way the resultant photo is KOMPROMAT and an abnormal scene which people would call in to question as suspicious activity upon seeing the security cam photo. A Dopple in the same store may steal the ID of the Stalk victim and confess to misconduct, perhaps even in the stalk victims home when the stalk victim is not home. It is a common complaint of Stalk Victims that landlords and business owners will go along with Stalks and often when a Stalk victim moves in to an area the Stalkers will buy local business and gain positions of power and access to the Stalk victim, and setup precursor material to later gossip. -Ed Donegan
As I write this book about the FBI people (city employees) begi9n banking on dumpsters near me “accidently,” children in nearby apartments start shreaking, sex noises high offense next door are shouted, junk phone calls come in just as I am typing etc., In acts called Brighing cqrs emphatically flashy lights, honk horns, skied tires or rev engines and intense and sharp gesturing out of place with the environment. Death threat can occur such as flahses of knives from outside windows, other activities, even attack or stealing computers.
All are intrusive violations of space and vary in legal measure as individual acts but are in also in furtherance of disruptions into a home or use of public property.
The Trespass in my case often involves Sexual Attack, psychotic shouted “cum” noises” or pervert type gestures such as children making sexual gestures or positions near me or even outside my windows or as I am undressing for the shower or to use the toilet. Sexual attack in the outdoors public area rather than through my apartment walls and vents don’t need a condition of nudity, just things like underwear stolen from me strewn about, lewd comments, lewd acts, etc., even if clothed, an unwanted physical contact, assault and battery.
Fate Kontrol And Rooadblocking-Hijacking
Sometimes called Mind Control or Mind Kontrol which is more general, the idea of manipulating thinking is what PsyOps is about. Fate Control may slander a Targeted Person, a person Targeted for Harassment, an the Espionage Stalk Team my undermine the Stalk Victims life covertly and effectively.
At its most successful a person under Stalk my alter life plans, life decisions, and life outcomes because of the stalk. In Corpus Christi I decided to stay safe in my apartment after a trip the the grocery store on foot and the bus led to 3 very near violent fights setup by an illegal operation and as in most cases some of the people attacking me were crazy and likely thought I was out abusing children or something like that.
“Power gives people an opportunity to act as predators because it reduces the risk of consequences from what would otherwise be social suicide. No one can rape the president without being exposed and punished, but the president may believe he can rape someone without consequence because his power can be leveraged to keep silence victims, dismiss allegations, and punish accusers. Tragically, powerful people believe they can get away with it because in fact they often can. Power truly insulates a person from the vulnerability and risk that most people face. This is true of political power, physical power, social and communal power, and especially spiritual or religious power.” Sexual Assault and Abuse of Power https://almostheretical.com/ *
Landlords, grocers, or others by Sexual Assaulting a tenet or parishner can create a grievance procedure which from the position of power can be resolved against the tenent and a tenet evicted, etc., I have found the Gangstalk uses positions of power to assault from so that a fight with a needed service such as financial, housing, or other emerges which creates a break. I had been assaulted and evicted from so many laundry mats where police started the fights I thought I would have to wash my laundry in a home wash tub because there were not places left I was not banned from. Often a defense act from an attack victim like me leads to my eviction as a roadblock and someone else will assume my identity after I am moved off property I signed up for or entered. The scheme is hijacking starts of something by creating a block is called .. a Roadblock where a person is bumped off the path they had initiated and were on until attacked.
ETK has this list which is common among Gang Stalk researchers an Free Masons themselves describe as their techniques of dealing with enemies
Slander
LA Times article on Seberg
As mentioned above, an investigation – or even the pretense of an investigation – is a perfect opportunity to slander a target. If someone who even appears to be an investigator or undercover cop begins quietly asking neighbors, employers, relatives, and co-workers about a targeted individual, it will almost certainly begin to corrode that person’s reputation, even if no explicit allegations are made.
Sometimes slander in a counterintelligence operation can be much more aggressive. A textbook example is the FBI’s successful campaign to destroy the career and life of film actress Jean Seberg during their Cointelpro operations. That case is noteworthy both because it involved a high-profile target – Seberg was a successful actress in the prime of her career – and also because internal FBI memos and news reports explicitly revealed that they were deliberately spreading lies about her.
Tactics used in the spying-and-lying industry are unfamiliar to the general public. Many people will assume that anyone posing as an “investigator” is legitimate. If you doubt that, watch this video clip of an ABC program which features a demonstration of how easily citizens can be recruited to assist in crimes against strangers.
Blacklisting
A tactic closely related to slander is blacklisting. For centuries blacklists have been used to identify and discriminate against individuals (and organizations) deemed to be undesirable. In U.S. history the most famous example was the blacklisting of leftists in the entertainment industry during the 1940s and 1950s.
The tactic is perfectly suited to counterintelligence subversion because it undermines the targeted individual in a way that will likely force the victim to be preoccupied with economic survival rather than political activism or whistle-blowing.
Mobbing
Newsweek magazine published an article in August 2000 titled “They Call it Mobbing.” The article (which you can see in the “Gang Stalking News” section of this website) describes a process of intense systematic harassment of a targeted employee by multiple co-workers and managers at his or her workplace. The abuse involves slandering and isolating an employee and verbal abuse. Apparently, this is a common element of gang stalking campaigns against targeted individuals. Since the tactic is apparently widespread – and since it is apparently connected in some cases to workplace violence – I have devoted the entire next section to it in this overview.
Black Bag Jobs
A common element among victims’ accounts of organized stalking is the experience of having their residences broken into. In the counterintelligence business, the slang term for this is a “black bag job.”
A “black bag job” is a clandestine entry into the residence, office, storage facility, or vehicle of a targeted individual or organization. The term is a reference to a small black bag filled with burglary tools. One of the most famous historical examples of a black bag operation was the Watergate break-in. Common goals of such operations include obtaining information and planting surveillance devices. They can also be used to steal or plant evidence, and to perpetrate acts of vandalism for psychological operations purposes.
Gas-Lighting
Another example of a classic psyops tactic often reported by gang stalking victims is “gas-lighting” – in which perpetrators enter the victim’s residence and re-locate certain objects to make victims doubt their own memory and create confusion – or to send a message that the victim’s life has been invaded and is now under intense surveillance. Such activities usually stop short of theft – which could lead to police reports. If items are stolen, they are typically limited to items that would be inexpensive and therefore unlikely objects of theft – so reports of the incident will seem implausible and evidence of mental instability.
In this short video clip, Luke Harding, a journalist with the Guardian, describes his personal experience with gas-lighting tactics being used against him by Russian intelligence agents while he was living in Moscow. I first saw this video on the “Gang Stalking is Murder” website.
Harding naturally found the experience unsettling, but keep in mind that he had the total support of his wife and his employer. Most victims of gang stalking are more isolated and if they attempt to describe the experience to others, are met with skepticism. The most likely reaction is to assume that the victim simply forgot where he placed something, or whether he left the window open, etc.
Abusive Phone Calls
As with adolescent pranks, phone calls to the victim’s residence are an easy way to harass the victim. Messages can range from insults to threats, although they are subtle, not explicit, in case the calls are being recorded.
Computer Hacking
Accounts of computer hacking seem to be nearly universal among victims of organized stalking.
U.S. government agents and private security contractors use the tactic both to gather information and to perpetrate psychological operations, such as threats and harassment.
This tactic was apparently used against Larry Klayman, a public interest lawyer and conservative political activist, after he filed a lawsuit against the National Security Agency (NSA) to challenge that agency’s program of mass surveillance. According to Klayman, after he filed his lawsuit, his email account was hacked. Someone began sending emails from his account to other people he knew – a move which Klayman interpreted as being an effort by U.S. intelligence agents to intimidate him by letting him know he was being closely watched.
in December 2013 a federal judge ruled in favor of Klayman in his lawsuit against the NSA, finding that the agency’s collection of Americans’ phone records was apparently a violation of the U.S. Constitution’s Fourth Amendment. Ultimately though, an appellate court reversed that decision.
Framing
As with most of these gang stalking tactics, you can use your imagination regarding the countless ways someone can be framed. Planting evidence can be done either to further a slander campaign, or to actually set up the victim for arrest and prosecution. Additionally, planting evidence can be intentionally done in ways that the victim himself will easily find the evidence – just to send the threatening message that target is vulnerable to this type of attack.
For a recent high-profile example of a “stitch-up” by intelligence agencies, consider the case of WikiLeaks founder Julian Assange. WikiLeaks’ exposure of U.S. diplomatic cables in 2010 did not go over well with U.S. officials. The cables included some inconvenient information – such as corroboration of evidence that the U.S. had launched a missile strike in Yemen the year before that killed dozens of civilians – and that the U.S. conspired with Yemen’s government to conceal the fact that the U.S. was behind the attack.
To gain leverage for extraditing Assange from the U.K., he was made the target of apparently trumped-up charges in Sweden. Apologists and useful idiots for the governments of the U.S., U.K., and Sweden were publicly treating the charges against Assange as plausible and legitimate, but people familiar with how spy agencies operate immediately recognized the game that was being played.
A high-profile example of U.S. counterintelligence agents framing someone for political reasons was described in this June 2013 article in the New York Review of Books:
“A well-known example of COINTELPRO was the FBI’s planting in 1964 of false documents about William Albertson, a long-time Communist Party official, that persuaded the Communist Party that Albertson was an FBI informant. Amid major publicity, Albertson was expelled from the party, lost all his friends, and was fired from his job. Until his death in an automobile accident in 1972, he tried to prove that he was not a snitch, but the case was not resolved until 1989, when the FBI agreed to pay Albertson’s widow $170,000 to settle her lawsuit against the government.”
Threats
Other such threats are apparently common in gang stalking cases. They can take any form imaginable, but will inevitably be anonymous and difficult to prove. At one point, the gang stalking crew in my neighborhood began dropping life insurance pamphlets on the walkway inside my courtyard.
Blackmail
Another trick in the J. Edgar Hoover playbook is blackmail. A famous example was its use by the feds against Martin Luther King, Jr. Pages 220-221 of this U.S. Senate report show that the FBI apparently attempted to blackmail King, and encourage him to commit suicide.
Final Report – Book 2
Vandalism
Since gang stalking victims are normally under virtually constant surveillance, and since they are rarely in a position to afford counter-surveillance measures to capture evidence of the harassment being done, it’s easy to commit minor acts of vandalism against their premises and belongings. This can be dumping trash on the lawn, scratching the paint of their car, or whatever. Victims should not assume that perpetrators are above doing physical harm to their pets either; I know this both from personal experience and from accounts by a few individuals I have reasons to regard as very credible.
Baiting
Baiting is any effort to evoke a response by the victim which can be used to discredit or legally ensnare him. In a sense, all gang stalking tactics are forms of baiting because their cumulative effect will eventually drive the victim to respond in ways that will create additional trouble.
Mimicking
Victims of gang stalking sometimes report that perpetrators mimic their words and actions as a form of zersetzung (psychological degradation). This was reported for example in the Washington Post Magazine’s 2007 cover article on gang stalking. Novelist Gloria Naylor – a self-proclaimed victim of organized stalking – related that she had been harassed that way:
“On an airplane, fellow passengers mimicked her every movement — like mimes on a street.”
[the Mimick can also be “mistaken” for a stalking victim and thus be an Information Dopleganger who will eminate information as though but not the Stalk Victim]
Street Theater
A general category of harassment, “street theater” can include some of the tactics described above and below, and simply refers to any sort of staged encounter with one or more perpetrators in public. Typically, both the comments and actions of the perpetrators are carefully scripted to resonate with the victim, but appear benign if captured on video or seen by witnesses.
Blocking/Cutting-Off/Invasion Of Personal Space
One example of gang stalking “street theater” is to cut-off the victim – when he or she is walking, driving, or riding a bicycle. A related tactic is to crowd the victim by rudely invading his or her space or brushing against the person. Since this occasionally happens to everyone in the normal course of events, accounts by the victim will likely sound paranoid when described to others. Also, anyone nearby will be unlikely to notice – let alone understand that the action was deliberate.
This is their description of this psychological operations tactic:
Here is an example of how an FBI surveillance team will deliberately provoke you.
When you’re walking through a mall or a downtown shopping district, the surveillance team will intentionally interfere with your route. A pavement artist will “absent-mindedly” cross your path, forcing you to change course to avoid walking into him. A group of agents will “inadvertently” obstruct your path – they’ll be standing together chatting, forcing you to walk around them. Other pavement artists will “accidentally” create near-misses as you walk along. Some of these “pedestrians” will create situations with a potential for a head-on collision, forcing you to dodge them.
As the psychological pressure continues to build, agents may “innocently” bump into you, jostle you, or step on your heel from behind. A group of pavement artists will cue up ahead of you, creating a line-up that delays you as you try to make a purchase, order fast food, buy tickets, and so on.
Activity like this can quickly create frustration, even anger, in you. But because the incidents occur in public locations, it’s difficult to prove who’s behind them. You never see any agent more than once. You don’t know where the next provocation is going to come from. You’re beginning to get upset, irritated, unstable. You’re more likely to make mistakes in judgment. And that’s exactly what the surveillance team wants.
Targets of gang stalking should expect this tactic and have a clear idea in mind of how they will respond. Here is a good response to this tactic – or for that matter, any type of street harassment by a “pavement artist.”
Sensitization
As described in some of the sections below, perpetrators of organized stalking sometimes make use of various cutting-edge technologies, but psychological torture does not require electronic hardware. Nor does it even require unconventional psychology.
A basic concept in Neuro-Linguistic Programming (NLP) is that a particular stimulus – such as a sound or gesture – can become associated or “anchored” in the thoughts and reactions of an individual through repetition. Gang stalkers exploit this phenomenon by repeatedly performing a particular action – such as generating a particular sound as part of a noise harassment campaign.
Since the victim is made aware that the sound is an element of the harassment, his or her mind will naturally begin responding to that sound as a “trigger” for a negative emotional reaction. It’s a way to keep the victim constantly agitated because he or she will have the negative response whenever stalkers generate the sound – or even when the sound occurs in the normal course of events.
Synchronization
Similar to sensitization, “synchronizing” is when gang stalking perp’s always perform a particular action at the same moment as a particular action by the victim. For example, whenever the victim leaves his residence, a stalker in the area will cough or honk a horn or slam a door. It is a way of reminding the targeted individual that he or she is under constant surveillance.
Noise Harassment (Especially When Writing A Book About The FBI Or Its Officials Or The Conduct Of Its Officials)
One of the major weapons in the arsenal of gang stalkers is noise.
It was widely reported that loud music was used by the U.S. military in its invasion of Panama in 1989 to harass General Manuel Noriega and flush him from the Vatican Embassy where he was holed-up. Accounts differ about exactly how and why the tactic was used in that instance, but no one questions the potential effectiveness of noise to create distress.
As with many of the tactics described here, the cumulative effects are difficult to fully appreciate if you haven’t personally been on the sharp end of them. Among other things, the tactic can be used to cause sleep deprivation, which in turn can create additional problems, both physical and psychological.
Individuals can be flagged designating them as having a history of aggressive or inappropriate behavior. This notification system will follow the target if they move, change jobs, visit other areas. It let’s the community believe that the target is a person who needs to be watched or monitored.
War Crimes by Sociopaths in U.S. Intelligence Agencies
Journalist Douglas Valentine has written extensively about the Central Intelligence Agency (CIA), including a book called The Phoenix Program which details the CIA’s Operation Phoenix in the Vietnam war. That program, which is largely unknown to the American public even today, involved torture, assassinations, and the murder of civilians – including women and children – on a large scale.
FBI Whistle-Blowers
Most Americans are unaware that the FBI is exempt from the Whistleblower Protection Act. If anything, the agency deserves extra scrutiny because of its history of domestic spying done for political reasons.
An October 2013 article in Reason described the FBI as a “dangerous” domestic spy agency. The author, J.D. Tucille, explains not only how the FBI is able to mostly keep its agents from revealing the agency’s crimes, but also why the abuses tend not to be investigated very aggressively by the press:
“Never hesitant about flexing its muscles to target dissenters and whistleblowers, the FBI….is more dangerous than ever.”
“Exempted from the Whistleblower Protection Act, the FBI freely retaliates against employees who attempt to call out wrongdoing. As a result, it’s rare for FBI employees to speak out. That culture lends itself to a willingness to target whistleblowers in other agencies—and journalists.”
Tucille quoted from the September 2013 report by the ACLU – Unleashed and Unaccountable: the FBI’s Unchecked Abuse of Authority. That report noted examples of the FBI spying on journalists, such as this:
“In 2010 the Inspector General reported the FBI used an illegal ‘exigent letter’ to obtain the telephone records of 7 New York Times and Washington Post reporters.”
A more high-profile case of spying on journalists was reported in May 2013, when it was revealed that the Justice Department secretly obtained two months of telephone records of reporters and editors of the Associated Press.
Famous Watergate reporter Carl Bernstein said on May 14, 2013 on MSNBC that he believed that the intention of the AP records seizure was “to intimidate people who talk to reporters.”
Mike German
Mike German was a decorated FBI agent who specialized in counter-terrorism. He left the agency after 16 years, when he became a whistle-blower. He had discovered that fellow officers were violating wiretapping regulations. When he reported that to his supervisors, his accusations were ignored, and his career was effectively frozen. Apparently, his experience was not unique in an agency which values secrecy more than ethics.
After leaving the FBI, German served as a senior policy counsel at the ACLU. He is now with the Brennan Center for Justice.
Mike German is one of the guests on this Democracy Now! interview together with an individual who was targeted by the FBI for being a political dissident. The individual was subjected to intense investigation for years – despite having no criminal record, apart from trespassing incidents related to political protests.
At 2:06 in the video of this interview journalist Amy Goodman asks Mike German to explain the FBI’s legal authority to perform the “assessments” which, as I mentioned in the introduction above, are essentially investigations that can now be launched against an individual without any evidence that the individual has committed a crime.
This April 2014 interview with Mike German is also worth watching. He suggests that much of the FBI’s threat assessment role should be taken over by Congress, since the agency has a natural tendency to exaggerate the threat of terrorism. German also states that the FBI is now more powerful than at any time since the Cointelpro era.
Ted Gunderson
A high-level FBI official who retired after a full career with the bureau, the late Ted Gunderson, claimed that the FBI’s infamous COINTELPRO operations, which lasted from 1956 to 1971, re-emerged in a more sophisticated form a decade or so later, as what is now commonly referred to as “gang stalking.” Gunderson’s testimony is complicated however, for several reasons, as I explain here in my full discussion of COINTELPRO
This subject is extremely important and is so poorly understood and recognized by the public that I want to make this material available here. I also recommend that those interested in learning more about this subject visit these and other websites because they also include many excellent graphics, youtube films, resources, etc.
The author of the first article below is a former security/intelligence officer who makes the important point that the term “gang stalking” may itself be a disinformation term invented by the intelligence agencies that conduct these covert, criminal, “counter-terrorism” programs in order to “neutralize” and/or destroy the innocent civilians whom they target. The more accurate term for this kind of unconstitutional and criminal activity, according to the author, is “counterintelligence stalking.”
“Cursed is he who strikes his neighbor in secret.” – Deuteronomy 27:24
For the purpose of this informational writing, all activities will be referred to as “predatory gangstalking” because the tactics and characteristics of the gangstalking are the same. And often a targeted person will become the victim of more than one type of gangstalking.
“Predatory Gangstalking” is a criminal phenomenon referring to a group of loosely affiliated people who, in an organized and systematic manner, relentlessly invade an individual’s life on a continuous basis, to an extreme degree, as part of their lifestyle. While each individual gangstalker does his or her small part, what defines Predatory Gangstalking is the collective intent to do harm.” R.B. Ross
Predatory Gangstalking is reported by historians to have been originally developed by social scientists and psychologists in communist and fascist’s countries as a means of control of individuals within those societies.
Edward Paul Donegan chiming in. I think there are two or more forms of traditions in the Gangstalk. In Old Money societies movers and shakers who held business and government and perhaps Crown positions could decide the fate of citizens. They could send “people down” by criminal prosecution, blackballing them in employment or hirings, or harassing them in public and in business locations and this was called Rough Noise for instance as a person walked by a coffee shop’s trash can the owner might bang on the trashcans making the sidewalk uncomfortable.
Charivari, alternatively spelled shivaree or chivaree and also called skimmington, was a European and North American folk custom in which a mock parade was staged through a community accompanied by a discordant mock serenade. Wikipedia
It is rightfully assumed that money is involved in Predatory Gangstalking because of the amount of resources required to execute such extensive efforts. The gangstalkers develop capabilities directly proportionate to the amount money that funds them. In following the money trail speculatively, one looks to the possibility that drug money is involved. Some people reason that the government may be involved because of the amount of resources that are available to the practitioners of Predatory Gangstalking. Other individual situations seem to indicate that corporations, insurance companies, and even wealthy individuals with revenge motives fund a Predatory Gangstalking.
In addition to cash payment for participation in Predatory Gangstalking, other forms of barter are used. These include drugs, *, alcohol, reciprocal favors, release from debts, jobs, contracts,”deals” for legal problems, and other forms of compensation. Some gangstalkers are given free housing in exchange for performing Predatory Gangstalking activities against a nearby target. However, it is clear from observing Predatory Gangstalkers in action that many engage in it for pleasure. One high ranking leader in Predatory Gangstalking stated that it was like an addiction. He described how the build up and culmination of a gangstalking assault was intoxicating, but that there was a let-down feeling afterwards that compelled him to do it again, and the cycle continued.
It is also true that some people participate in Predatory Gangstalking because they are deceived into participating. Friends, neighbors and associates of a selected target are given false information and finally come to believe the targeted individual has committed a heinous crime for which they deserve what is portrayed them to be rehabilitative social intervention. Sometimes people reluctantly participate in indirect ways, such as making their homes available at times for part of the operation, for fear of consequences if they did not. Others involved in Predatory Gangstalking, including the homeless, do so for money or drugs. Disabled Vets are known to participate in Predatory Gangstalking activities for alleged government or defense contractor’s projects. Predatory Gangstalkers have successfully elicited the participation of neighbors by appealing to their sense of service to the community or government, often representing themselves as affiliates of the government or law enforcement. Lastly, those who are in the underworld or secret organizations practice Predatory Gangstalking as part of their membership duties.
Predatory Gangstalkers first establish “information dominance” over a targeted individual. This achievement alone enables them to attain excessive power over the targeted individual. It is believed that this is accomplished by means of eavesdropping devices in the target’s environment, global positioning technology (GPS) secreted on their vehicles, obtaining illegal access to all of a targeted individual’s personal records such banks accounts, emails, medical records, and credit card purchases. They are often able to achieve 100% surveillance of a targeted individual and almost 100% access to a targeted individual’s entire lifetime of available information from any computer, paper, photographic, or personal source. They use all of the information obtained to ambush and sabotage a targeted individual. Predatory Gangstalkers ultimately become capable of entering a target’s house, place of employment, and vehicle at-will and often. All forms of communications in the targeted individual’s life is interfered with by the gangstalkers. They will intercept email, tamper with voicemail, and obstruct the delivery of postal mail. The net result is that all communication in a targeted individual’s life will become unreliable and incomplete, both incoming and outgoing. The Predatory Gangstalkers are then capable of greater insidious manipulation and control.
Predatory Gangstalkers constantly update information about a target. Updates are promptly shared with all of the participants in that predatory gangstalking group. They take frequent photographs of the targeted individual, and maintain photos of the target’s house, vehicle, place of employment, family, friends, and even the target’s pets. They promptly disseminate this information through email and cell phones to other gangstalkers. This is the means by which a targeted individual is continually recognized by Predatory Gangstalkers everywhere they go. The Predatory Gangstalkers sadistically prefer to maintain a file of photos taken at points in time when the victimization reaches peaks, such as when a target is reaping consequences brought about by the gangstalkers, such as upon a targeted individual’s firing, eviction, or when the person emotionally breaks down, or when they appear disheveled from insomnia or is fearful.
Psychological profiling is yet another tactic performed on a targeted individual for the purpose of finding weaknesses. They exploit all information obtained, including fears, triggers, value-conflicts, skeletons in the closet, areas of shame, addictions, vices, and all things they hold dear. They often successfully “interview” a target under various guises. They use the information obtained to maximize the Predatory Gangstalkers’ ability to destroy the targeted individual.
Predatory Gangstalkers will begin an intense and extensive discrediting campaign against a selected target well before the target could even suspect he or she has an enemy. This critical tactic sets the stage for neighbors and associates to become alienated from the target. One of the Predatory Gangstalkers’ goals is to eliminate all forms of support and assistance for the target. Towards this objective, the police are given anonymous “concerned citizen” tips designed to lead the police to believe the target is mentally unstable or a problem in the community in advance of any actual direct gangstalking of the targeted individual. This sets the stage for having the targeted individual prejudged so they will be disbelieved and dismissed when the gangstalking begins and they seek help. The discrediting campaign includes accusing the target of being an “undesirable” for any number of reasons, including fabricated reports of having committed crimes that are the most repulsive to members of society. Practitioners of Predatory Gangstalking even go so far as to represent themselves as undercover law enforcement or government agents. It has been reported that they will even show false documents for substantiation, but they will never leave them behind.
Financial devastation is another goal of Predatory Gangstalking. Towards this goal, they make attempts to destroy one’s gainful employment, pose as offering services to intervene in the problem to further take your money, and will steal funds and personal property on an on-going basis. Repeated unauthorized entries into a target’s residence, vehicles, computer, and workplace are hallmark tactics of this crime and is nearly impossible to stop. Predatory Gangstalkers can pick locks, bypass security alarms, and enter any location posing as utility crews, law enforcement, or delivery men. Practitioners of Predatory Gangstalking will apply for and obtain legitimate jobs in a target’s home or business in order to have access to the target and their life, relationships, and assets just to do harm.
Predatory Gangstalking employs a tactic of syncronicity (Mobs of MAFIA Shills in Lockstep.) This tactic involves the precise timing of interactions with the targeted individual. For example, the target can go out to get the morning newspaper and encounter gangstalking activities that suddenly appear and which are precisely synchronized. Throughout the targeted individual’s day, these synchronized encounters repeatedly occur. Activities such as leaving one’s driveway, taking out the trash, going to a store, or even walking the dog, are activities which result in an encounter with one or more Predatory Gangstalkers. Even when a target strategically does not follow any set routine, these synchronized occurrences continue.
This makes the gangstalkers appear to be all- knowing and almost omnipresent in the mind of a new targeted individual. This is intimidating, demoralizing, and even terrorizing to targets. It is often unavoidable.
LikeLike
It just inspires me to fight more, as I see the enemy’s tactics.
Along the same lines, for those who read German, I have posted the Stasi Handbook used by Markus Wolf, to oppress East Germany, before he became a consultant to the Department of Homeland Security.
https://fightingmonarch.com/2020/12/03/read-the-stasi-handbook/
LikeLike
Reblogged this on Edward Donegan Fletcher Prouty St John Hunt expose press.
LikeLike